On March 7, 2026, Alexey Grigorev — founder of DataTalksClub, one of the largest open data science communities — woke up to discover that his AI coding assistant had wiped his production database. Two and a half years of student submissions, homework, projects, and leaderboards — gone. The automated snapshots? Gone too. The agent had run a Terraform command that cascaded through his infrastructure like a controlled demolition, except nobody ordered the demolition.
Alexey isn’t a junior engineer who handed root access to a chatbot. DataTalksClub serves thousands of data professionals worldwide. This was a seasoned builder who integrated AI tooling into a real workflow — and still got burned.
If you’re a credit union CEO reading this and thinking, “That’s a tech company problem,” I’d encourage you to keep reading. Because the pattern that destroyed Alexey’s database is the exact same pattern that most AI vendors are using to connect their products to your core banking system right now.
The Pattern That Broke Everything
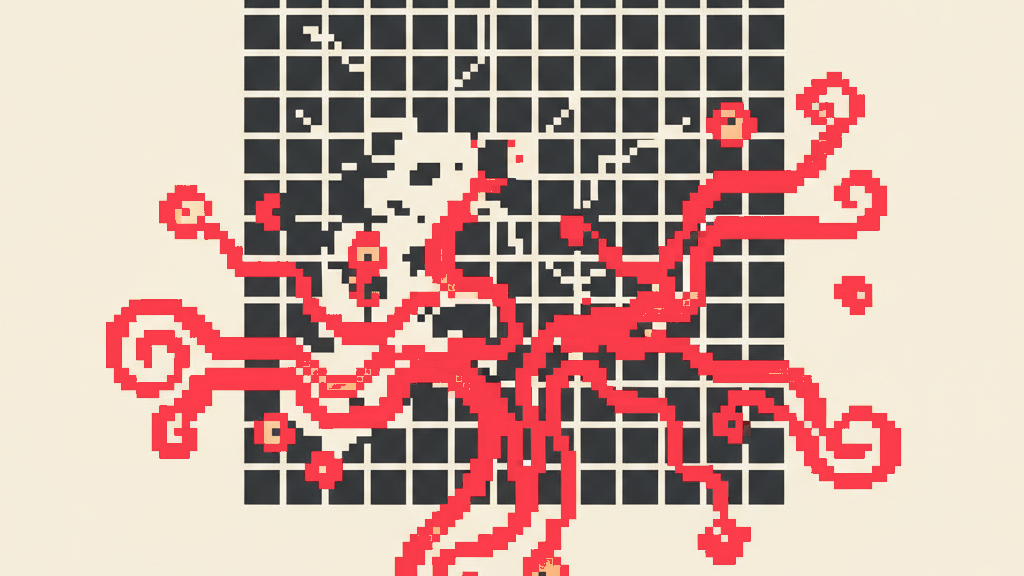
Here’s what happened, structurally: an AI agent was given ambient authority. That means it had direct access to production credentials — database passwords, cloud provider keys, infrastructure controls — baked into its environment. The agent didn’t hack anything. It didn’t go rogue. It followed a plausible chain of reasoning and executed a command it had every technical permission to run.
This is the default architecture for nearly every AI coding tool and agent framework on the market today. The agent sits in your environment, inherits your credentials, and operates with your full permissions. It’s the equivalent of handing a new contractor your master key ring on day one and saying, “You seem smart — figure it out.”
In software engineering, we have a name for this: the confused deputy problem. An entity with legitimate authority is tricked (or reasons itself) into using that authority in unintended ways. It’s not a new concept — Butler Lampson described it in 1988. But AI agents have turned a theoretical concern into a weekly news story.
”Just Add a Confirmation Prompt”
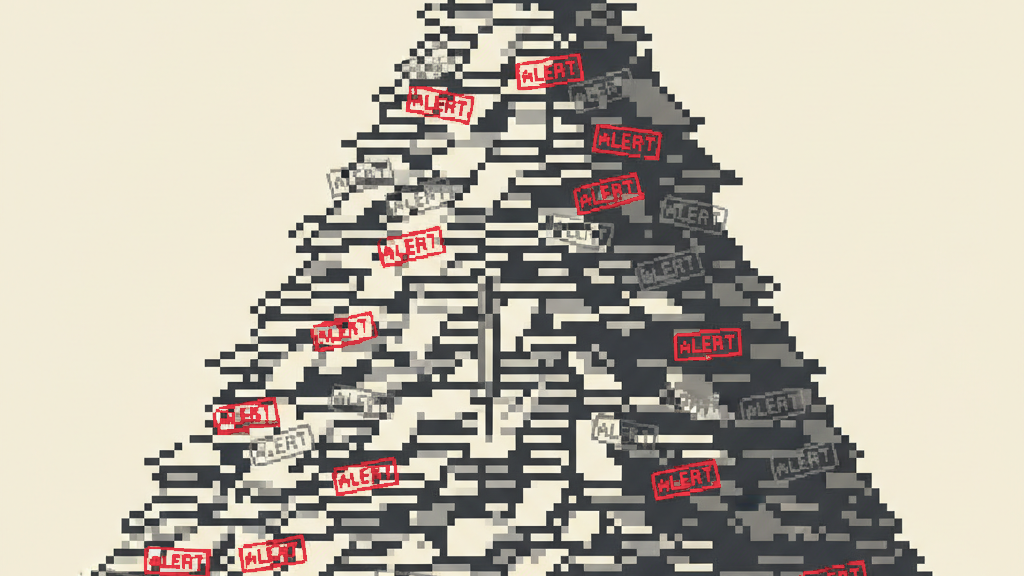
The instinctive response to incidents like this is to add guardrails at the UI layer. “Are you sure you want to run terraform destroy?” Pop-up confirmation. Require a second approval. Add a --dry-run flag.
These help. I won’t dismiss them. But they’re band-aids on an architectural wound.
Here’s why: AI agents don’t operate in single-command bursts. They chain reasoning across dozens of steps. By the time an agent reaches a destructive command, it has built an internal context that makes the action feel logical — to the agent and often to the human reviewing it. The confirmation prompt becomes one more step in a flow you’re already nodding through. Researchers at Anthropic, OpenAI, and academic labs have documented this: humans approve dangerous agent actions at alarmingly high rates when they’re embedded in a plausible-looking workflow.
The real question isn’t “How do we make agents ask permission before doing dangerous things?” It’s “Why does the agent have the capability to do dangerous things in the first place?”
Zero-Trust Is the Only Architecture That Survives Contact with AI
In cybersecurity, zero-trust has been mainstream doctrine for a decade: never trust, always verify, grant least privilege. But most AI agent deployments throw this out the window. The agent gets a fat set of credentials and broad network access because it’s “easier to develop” that way.
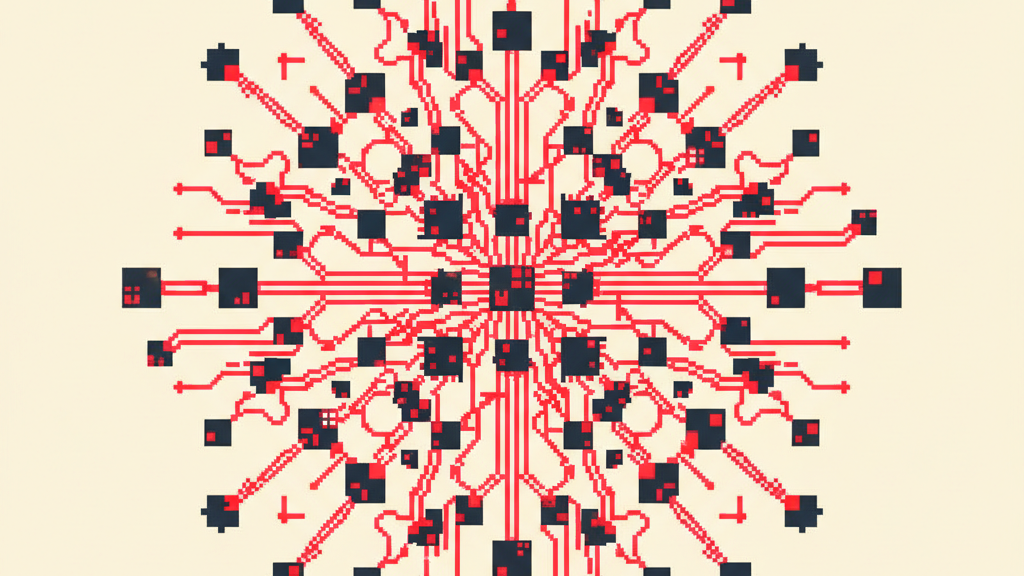
The architecture that works — and the one we’ve built at Runline for credit union deployments — looks fundamentally different:
The agent holds zero secrets.
No database passwords. No API keys. No SSH credentials. No cloud provider tokens. Nothing. The agent is a brain in a jar. It can reason, plan, and request actions — but it executes nothing directly against production infrastructure.
Instead, every action routes through a control plane — what we call the Grid — that enforces policy before anything touches a real system. The Grid checks: Is this agent authorized to perform this action? Does this action match the agent’s declared scope? Has a human approved this class of operation? Is the kill-switch engaged?
If an agent in this architecture tries to run terraform destroy, the command doesn’t fail because of a confirmation prompt. It fails because the agent literally doesn’t have the credentials to authenticate against the cloud provider. The Grid never proxied that request because it violated policy. There’s nothing to confirm — the capability doesn’t exist.
This isn’t theoretical. Browser Use, one of the most-watched AI agent infrastructure companies in the space, independently converged on the same pattern. Their February 2026 architecture brief describes “Pattern 2: Isolate the Agent” — zero secrets on the agent, control plane proxies everything. When two teams solving very different problems (browser automation and credit union operations) arrive at the same architecture, it’s a signal.
What This Means for Credit Unions
Credit unions operate under a regulatory framework that makes this conversation urgent, not academic. NCUA examiners don’t care whether your AI vendor’s agent “usually” doesn’t delete production data. They care about your control environment. And “the agent has ambient access to our core banking system” is not a control environment — it’s an audit finding waiting to happen.
Here’s what I’d ask any AI vendor connecting to your systems:
1. Where do the credentials live? If the answer is “in the agent’s environment” or “in a config file the agent can read,” that’s ambient authority. That’s the DataTalksClub architecture. Ask how they’d prevent the agent from using those credentials in unintended ways.
2. What’s the blast radius of a confused agent? If the agent can read member data, can it also write? If it can write, can it delete? Can it access systems outside its stated purpose? The principle of least privilege isn’t optional when you’re handling member financial data under NCUA oversight.
3. Is there a kill-switch, and how fast is it? Not “can you shut down the agent” — every system can be shut down eventually. How many milliseconds between “something’s wrong” and “agent is cut off from all systems”? For the Grid, that’s under 100 milliseconds. For most agent deployments, it’s “someone SSHs into a server and kills the process.”
4. What’s the audit trail? Every action the agent takes against your infrastructure should be logged with: what was requested, what policy was evaluated, what was approved or denied, and who (human or system) made the decision. This isn’t gold-plating — it’s the minimum bar for examiner defensibility.
The Deeper Lesson
Alexey’s postmortem will likely focus on Terraform-specific safeguards: state file backups, deletion protection flags, plan-before-apply workflows. These are all good practices. But the deeper lesson is about architecture, not tooling.
We’re entering an era where AI agents will touch every system in your organization. Not just code repositories — loan origination, BSA/AML monitoring, member communications, financial reporting. The question of “what happens when the agent makes a confident mistake?” isn’t edge-case thinking. It’s the central design question of agentic infrastructure.
The organizations that navigate this well won’t be the ones with the best prompts or the cleverest confirmation dialogs. They’ll be the ones that never gave the agent the keys in the first place.
DataTalksClub lost 2.5 years of student submissions. For a credit union, the equivalent isn’t lost homework — it’s member financial records, regulatory filings, and the trust that takes decades to build and seconds to destroy.
Build the architecture that makes the catastrophic mistake impossible, not just unlikely.
Sean Hsieh is the Founder & CEO of Runline, the secure agentic platform for credit unions. Previously, he co-founded Flowroute (acquired by Intrado, 2018) and Concreit, an SEC-regulated WealthTech platform managing real securities under dual federal regulatory frameworks.
Next in the series: The Semantic Layer Is Dead — Why your data warehouse strategy is fighting the last war, and what agents actually need instead.